Network Segmentation for the Production Floor: Protecting NWA Manufacturing Facilities

What Is Network Segmentation — and Why Does It Matter on the Production Floor?
In most Northwest Arkansas manufacturing facilities, the office network and the production floor share the same infrastructure. Email, ERP systems, CNC machines, PLCs, and security cameras all ride on one flat network. That’s a problem.
Network segmentation divides your network into isolated zones, each with its own access rules. If ransomware hits an office workstation, it can’t jump to your programmable logic controllers. If a compromised IoT sensor phones home to a command-and-control server, it can’t reach your accounting database.
For manufacturers in Bentonville, Rogers, Springdale, and across NWA, this isn’t theoretical. Production downtime from a network breach averages $260,000 per incident for mid-size manufacturers, according to IBM’s 2025 Cost of a Data Breach report.
The Flat Network Problem in Manufacturing
Here’s what a typical unsegmented manufacturing network looks like:
- Office PCs, printers, and guest Wi-Fi on the same subnet as production equipment
- SCADA and HMI systems accessible from any device on the network
- IoT sensors (temperature, humidity, vibration) with default credentials, reachable from anywhere
- No separation between vendor VPN access and core business systems
One phishing email. One compromised laptop. That’s all it takes to put your entire operation at risk.
How Network Segmentation Protects Your Production Line
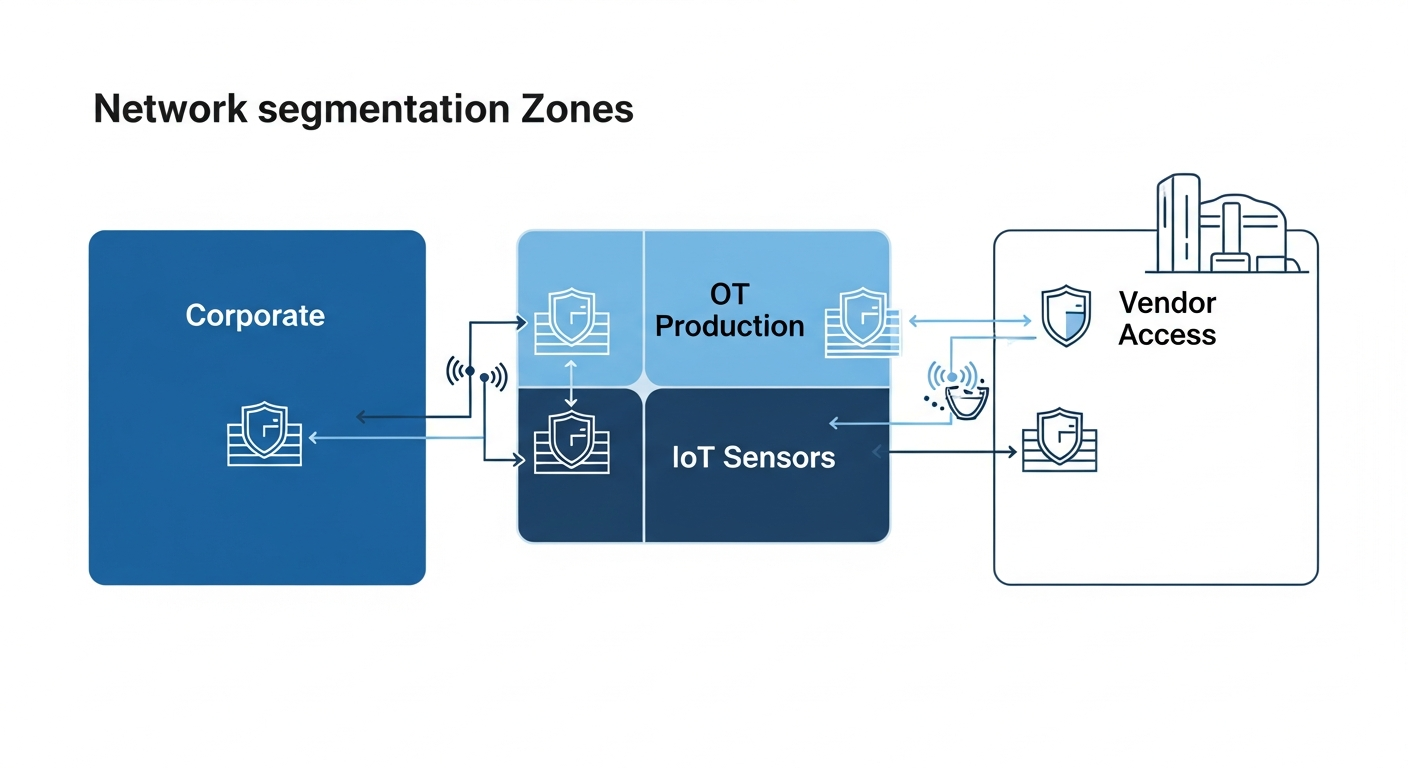
Proper segmentation creates distinct zones with controlled traffic between them:
Zone 1: Corporate IT — Email, file shares, ERP front-end, internet access. Standard security policies apply.
Zone 2: Operational Technology (OT) — PLCs, SCADA, HMIs, CNC machines. Restricted access, no direct internet connectivity, monitored traffic only.
Zone 3: IoT and Sensors — Environmental monitors, smart devices, cameras. Isolated with minimal permissions — they report data out but accept no inbound connections.
Zone 4: DMZ / Vendor Access — Third-party remote access, cloud integrations, and update servers. Tightly controlled, logged, and time-limited.
Between each zone sits a firewall with explicit allow rules. Nothing moves between zones unless you’ve approved it.
Real Benefits for NWA Manufacturers
Contain breaches before they spread. A compromised office PC stays an office problem — not a production shutdown.
Meet compliance requirements. NIST 800-82, IEC 62443, and many supplier security questionnaires require network segmentation. If you’re supplying Walmart, Tyson, or J.B. Hunt, this matters.
Improve network performance. Segmentation reduces broadcast traffic. Your CNC machines don’t need to process ARP requests from 200 office devices.
Enable safe remote access. Vendor technicians connect to the vendor zone only — never your production systems directly.
Getting Started: What to Do This Week
- Map your network. Identify every device, what zone it belongs in, and what it needs to communicate with.
- Prioritize OT isolation. Separating production equipment from the corporate network is the single highest-impact change.
- Implement VLANs and firewall rules. Modern managed switches and next-gen firewalls make this achievable without ripping out infrastructure.
- Monitor cross-zone traffic. Set up alerts for any unauthorized communication between zones.
- Document and test. Segmentation only works if the rules are maintained as your network evolves.
Don’t Wait for a Breach to Segment Your Network
Most manufacturers we work with in Northwest Arkansas don’t realize how exposed their production systems are until we run an assessment. The good news: segmentation is one of the most cost-effective security improvements you can make, often using equipment you already own.
QuanTech IT offers free network security assessments for NWA manufacturers. We’ll map your current network, identify critical vulnerabilities, and deliver a segmentation plan tailored to your facility — no obligation, no sales pitch.
Schedule your free assessment today or call us to get started.
